Cybersecurity buyers don't trust easily.
That's the whole point.
The people evaluating your product spend their careers identifying risk, spotting weak signals, and questioning what they're told. That same instinct applies when they land on your website.
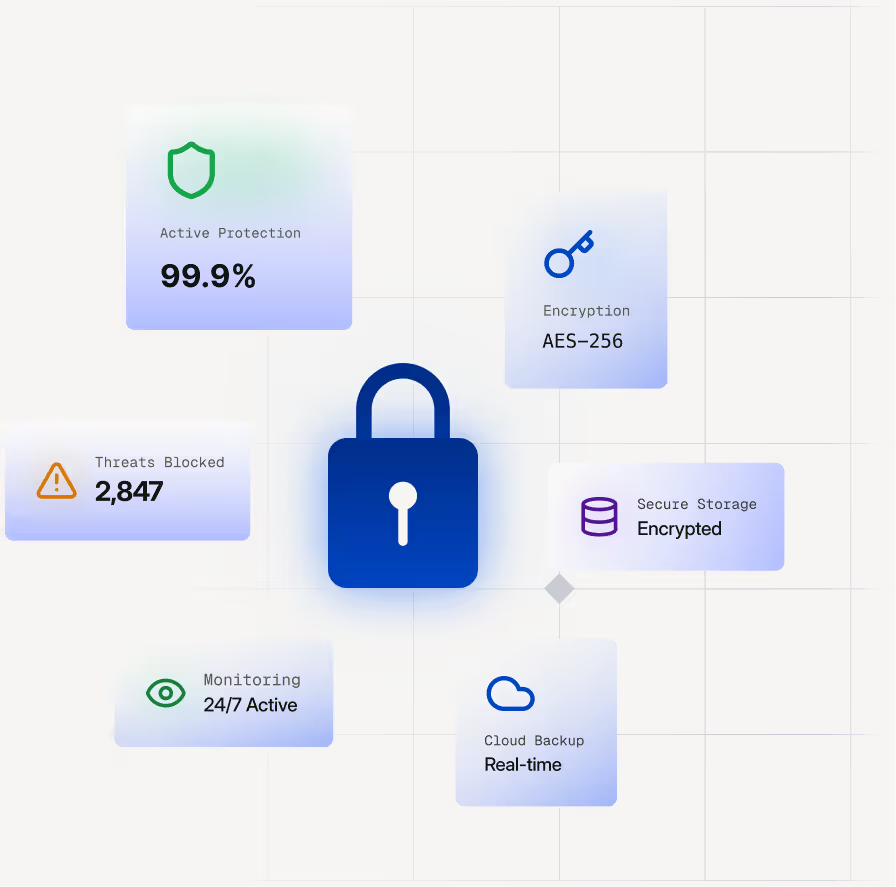
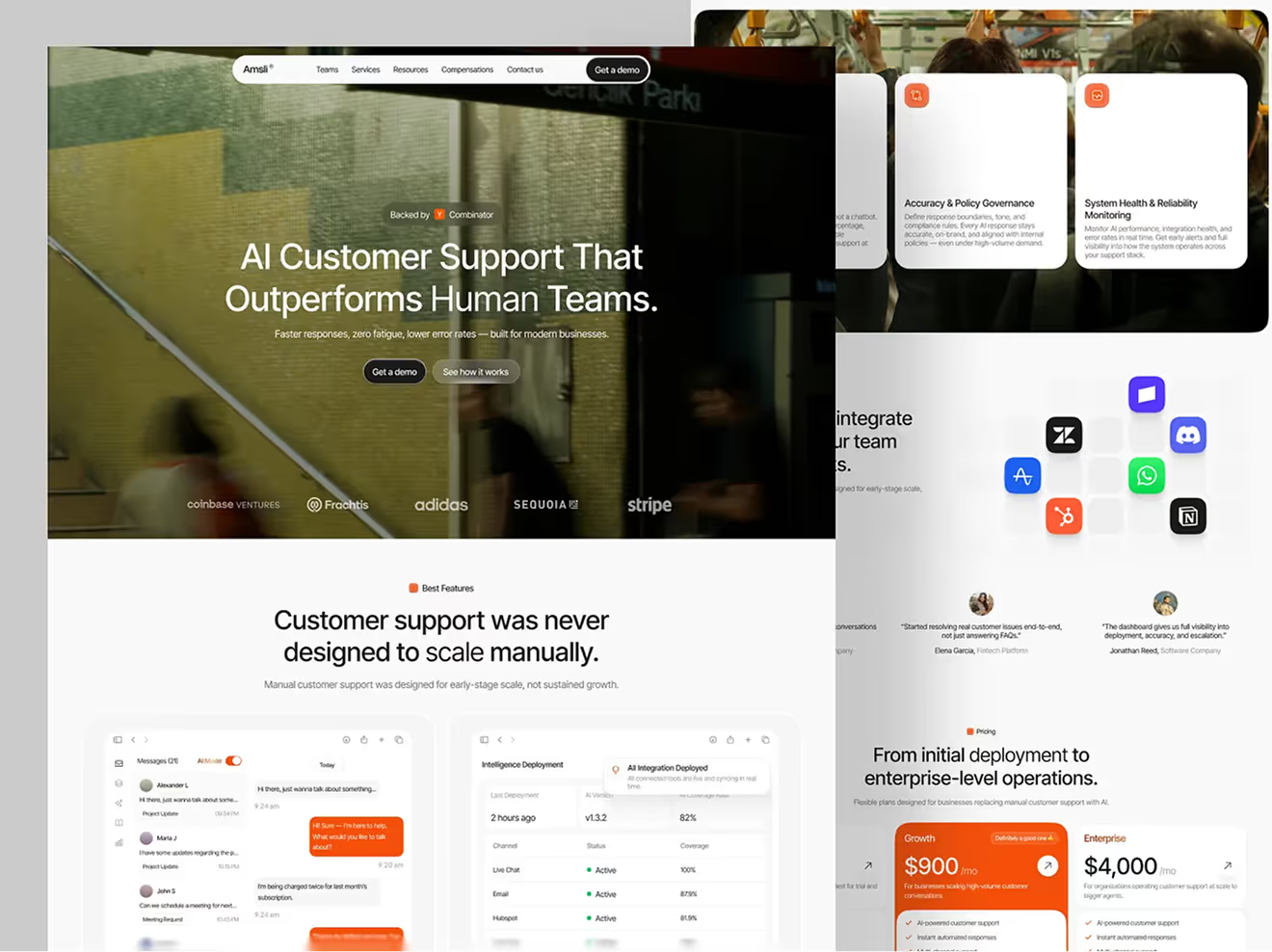
A generic design reads as a lack of attention to detail. Vague claims about "enterprise-grade security" or "end-to-end protection" read as marketing noise. And a site that looks like it was built in a hurry signals that your organisation cuts corners — which is exactly the wrong message in this category.
The good news is that the same rigour your buyers apply to threat assessment can be applied to your website. Specific language. Verified proof points. Clear explanation of how you work and what you protect against. A design that communicates precision rather than panic.
That's what we build for cybersecurity companies. Not a site that looks impressive. A site that holds up under scrutiny.
.svg)

.svg)
.svg)



![Portrait of a Kecin D Chen [Dark]](https://cdn.prod.website-files.com/6963b46b73d13c416619d604/696770db31b454394fd4709a_5bbdaf7344be9b801e9af82997f5e05f_kevin-photo.png)
%203.avif)
.avif)
.avif)
.avif)
.avif)